Your mobile and enterprise app projects delivered
Starting a new venture, finishing a challenging project or supporting a legacy system, demands a software development partner you can rely on.
For businesses and organisations just like yours
Whether you’re the IT manager swamped with a backlog of features to deliver, the CEO looking to grow your business, an investor looking for development resource to a get a vision brought to reality, or a quality manager drowning in support tickets, Microsec has the design, development and delivery know-how to take away the burdens of building, managing and supporting today’s software.
- Large corporates
- Medium enterprises
- Small businesses
- Non-profit organisations
- Startups
- Retail
- Financial services
- Government
- Educational
- Healthcare
- Manufacturing
- Media
- Consultants
- Investment
- and more…
- Design, development and management resources on tap
- Custom teams of experienced technology professionals
- Mobile and web app development managed to your budget
Do you struggle to deliver products and services customers love?
-
Products continually need redesign after release?
-
Outsourced development partners let you down before?
-
Are you continually firefighting unexpected issues?
-
Are you struggling to communicate your vision?
-
You don't have enough skills in-house to deliver on time?
-
Do you struggle to manage the backlog of product defects?
Work with Microsec and deliver products your customers can rely on
Start your projectHow we work with you
We focus on getting the best experience for users and the best value for your business
What clients say about working with us
Working with Microsec, we'll be teaming up with you from start to finish. And even when the project is delivered, you'll know you can come back to us at any point for support, advice, and developing new business.
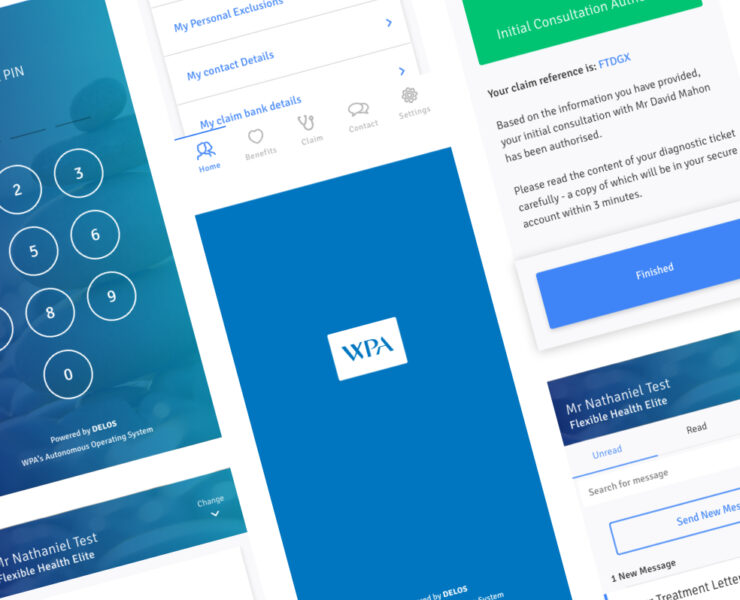
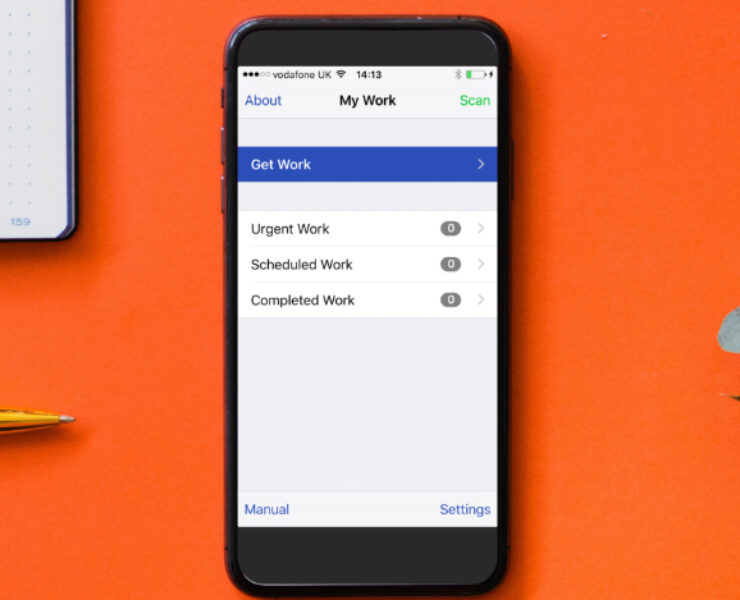
Start your projectSome of our work
Solving tough technical challenges and delivering finished projects to our customers
Built up over 40 years across a broad range of industries, our experience, skills and reputation is a formidable combination we’re confident can be applied to any software development project
Start your projectStart your project conversation
Application and mobile development should be a lot easier. We can help.

What you can expect when we talk
In just 30 minutes, we can give you valuable advice, for free, with no obligation
First we listen, really carefully
All projects are unique and we want to understand exactly what you want to achieve, before we suggest anything. We’ll ask a few key questions about your organisation, target customers, software requirements and key objectives.
We’ll talk about Microsec expertise
We have a wide range of services in design, development and management, so we want to make sure there’s a good fit between your needs, and the specialist skills, experience and resources we can offer.
We’ll plan next steps together
If at the end of our initial conversation you think Microsec is a good match, we’ll suggest some further activities, such as a discovery workshop or project analysis, and put your key people in touch with our specialists to get things moving.